OPC UA in OT Environments and ICS Cybersecurity – A Narrative Guide for Engineers

Introduction to OPC UA
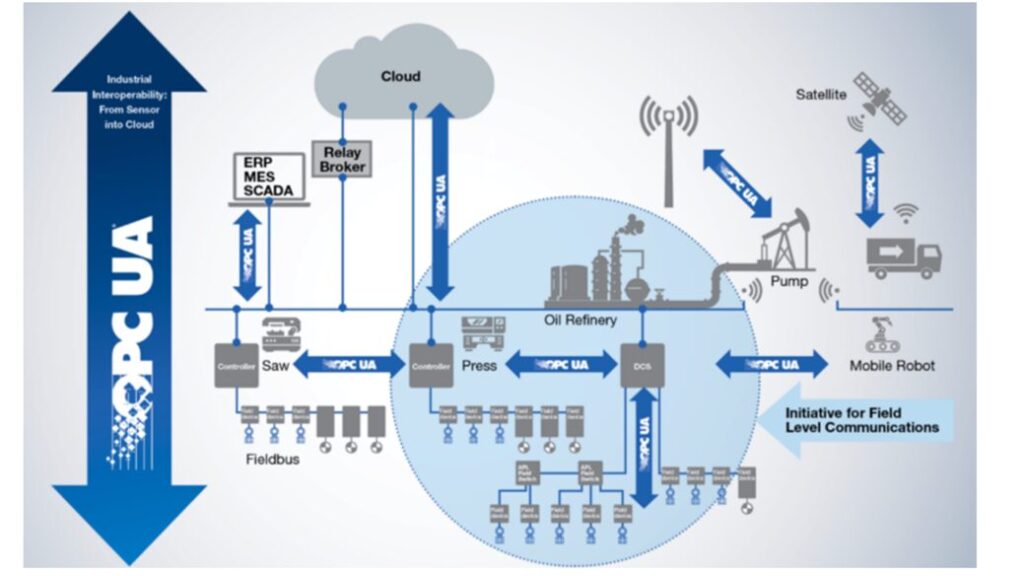
Integrating Open Platform Communications Unified Architecture (OPC UA) into Operational Technology (OT) environments is akin to a renaissance in the tapestry of industrial automation. This evolutionary stride transcends the realm of mere technological advancement, emerging as a strategic beacon in the turbulent seas of cybersecurity threats. As the threads of digital connectivity and intelligent automation weave into the fabric of industrial operations, the incorporation of OPC UA within OT systems heralds not just a leap in efficiency and interoperability but a bulwark fortifying these systems against the insidious tendrils of cyber vulnerabilities.

This treatise ventures deep into the labyrinth of OPC UA within the context of OT environments. It seeks to illuminate this advanced communication protocol’s intricate pathways and hidden nooks, exploring its symbiosis with existing and burgeoning industrial systems. The narrative rests not solely on understanding the anatomy of OPC UA and its functionality within these environments but also on a comprehensive excavation of its implications for Industrial Control System (ICS) cybersecurity.
OPC UA is not merely a protocol; it is the ligament connecting the disparate limbs of industrial automation, a secure, reliable, and standardized conduit. It plays a cardinal role in the alchemy of transmuting raw data exchange and communication between diverse industrial systems into the gold of Industry 4.0. Yet, with this greater interconnectivity comes a shadow of vulnerability, as the sophistication of cyber threats looms large, challenging the safety and integrity of critical industrial operations. Thus, understanding and implementing robust ICS cybersecurity measures in concert with OPC UA is not a matter of choice but a necessity.
This article, crafted meticulously, aims to be an enlightening beacon for network experts, engineers, and cybersecurity mavens. It endeavors to impart a profound understanding of OPC UA’s role in OT environments, the burgeoning cyber threats, and the rational practices in ICS cybersecurity. By juxtaposing the opportunities OPC UA presents against the challenges sculpted by the cyber threat landscape, this narrative aspires to empower professionals with the wisdom and tools necessary to navigate this evolving domain adeptly. The goal is twofold: to augment operational efficiency and reliability and to forge an unbreakable shield ensuring the resilience and security of industrial systems in our increasingly interconnected and digitized epoch.
Understanding OPC UA in OT Environments
OPC UA as a standardized communication protocol in Industrial IoT Solutions.
What is OPC UA?
OPC Unified Architecture (OPC UA) is a beacon of revolutionary advancement in machine-to-machine communication, particularly in industrial automation. Birthed by the OPC Foundation, a guild dedicated to crafting and stewardship of standards for open connectivity in industrial automation devices and systems, OPC UA distinguishes itself with a robust, secure, and flexible architecture.
Core Design Principles of OPC UA
Secure Communication: At its core, OPC UA has been meticulously forged with a strong emphasis on security. It is armored with advanced security models encompassing encryption, data signing, and authentication mechanisms. This ensures that the data exchanged between devices and systems is shielded from unauthorized eyes and remains intact and trustworthy.
Reliable Data Exchange: Reliability is another cornerstone of OPC UA. It is imbued with mechanisms to ensure consistent and dependable communication, even in the face of network tumults or device failures. This reliability manifests through redundant server configurations and buffered data handling.
Platform Independence: OPC UA’s platform-independent nature is a significant boon. Unshackled from the confines of its predecessor, OPC Classic, primarily tethered to Windows-based systems, OPC UA can traverse various hardware platforms and operating systems. This flexibility unfurls a vast tapestry of possibilities for integration and interoperability in diverse industrial landscapes.
Advanced Functionalities of OPC UA
Complex Data Types: OPC UA is adept at handling complex data types, enabling it to manage more sophisticated data structures than mere numeric values or text strings. This ability is crucial for conveying nuanced and structured information about industrial processes, be it the status of a machine or the nuanced readings from a multi-faceted sensor.
Event Handling and Alarm Notifications: OPC UA transcends mere data exchange. It boasts a robust event-handling system that monitors and notifies specific events within the industrial process. This feature is a sentinel of operational efficiency and safety, enabling automated responses to specific conditions, like sounding an alarm when a machine veers from its ordained parameters.
Modeling and Semantic Information: OPC UA also unfurls the canvas of information modeling. It allows the depiction of complex data and relationships in a standardized manner, essential for the tapestry of Industry 4.0 and the Internet of Things (IoT). This semantic layer ensures that data is exchanged and comprehended in context, paving the way for more intelligent and integrated industrial systems.
OPC UA represents a significant leap forward in the annals of industrial communication protocols. Its design ethos centers around security, reliability, and platform independence, while its advanced functionalities, such as complex data types, event handling, and semantic information modeling, render it an indispensable tool in the modern alchemy of industrial automation and control systems. By embracing OPC UA, industrial realms are optimizing their operations and charting a course toward more sophisticated, interconnected, and intelligent automation systems.
Role of OPC UA in OT
In the grand theatre of industrial automation and integration, the role of Open Platform Communications Unified Architecture (OPC UA) in Operational Technology (OT) is a performance pivotal in shaping the future. As a comprehensive protocol, OPC UA plays the protagonist, harmonizing various industrial hardware and software, laying the foundation for advanced data exchange and interoperability. This section delves into the multifaceted role of OPC UA in OT, spotlighting its significance in orchestrating seamless communication among diverse systems and driving the narrative of Industry 4.0 initiatives.
Bridging Diverse Industrial Systems
Interoperability with PLCs, SCADA, and MES:
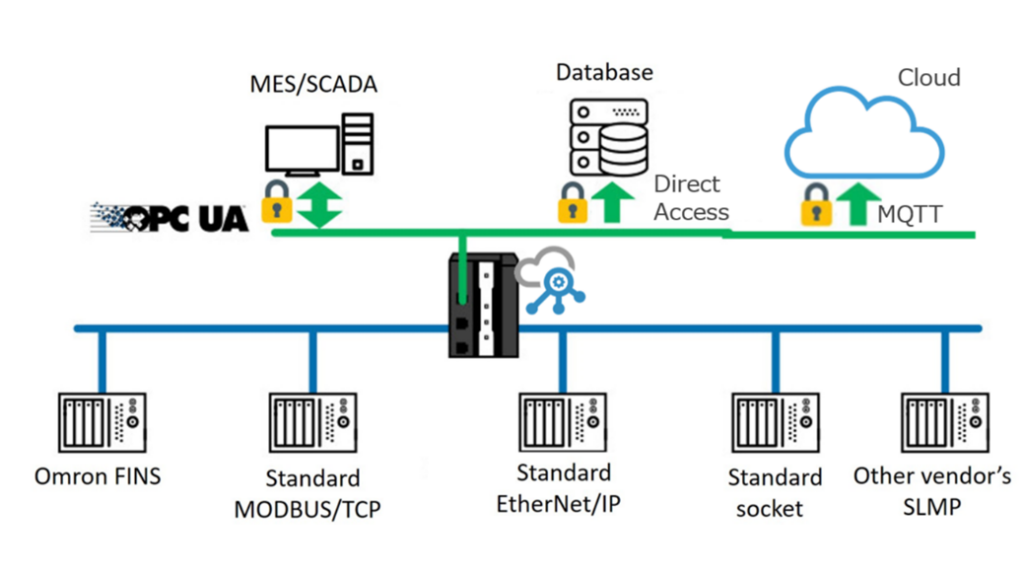
Programmable logic controllers (PLCs) are the heartbeats of many industrial processes, control machinery, and plant operations. OPC UA facilitates communication with other systems, transcending brand and model differences. This universality allows for real-time data acquisition and control, enhancing the choreography of process automation and efficiency.
Supervisory Control and Data Acquisition (SCADA) Systems: the watchful eyes overseeing industrial processes across vast expanses and sites, SCADA systems find an effective medium to communicate with field devices and PLCs in OPC UA. This ensures that their data is timely, accurate, and actionable.
Manufacturing Execution Systems (MES): MES, the maestros managing the production process from raw materials to finished goods, find harmony in OPC UA’s role in integrating them with other control systems. This ensures that the symphony of production data aligns with operational data, enabling more efficient and optimized manufacturing processes.
Standardizing Data Exchange
Unified Communication Protocol: OPC UA standardizes the language of system communication, eliminating the need for custom interfaces or proprietary solutions. This standardization simplifies the integration process, reduces development time, and minimizes errors.
Data Consistency and Accuracy: By providing a common language for data exchange, OPC UA ensures that data is consistent and accurate across different systems. This is crucial in the intricate dance of complex industrial environments, where discrepancies in data can lead to operational inefficiencies or even safety hazards.
Facilitating Industry 4.0 Initiatives
Enabling Smart Operations: The adoption of OPC UA is instrumental in realizing the vision of smart factories and Industry 4.0. It allows the integration of IoT devices, providing the backbone for data-driven decision-making and intelligent automation.
Data Integration and Analysis: OPC UA plays a vital role in aggregating data from various sources for analysis. This integrated approach enables more profound insights into operational efficiency, predictive maintenance, and process optimization.
–Scalability and Flexibility: As industries evolve and new technologies emerge, OPC UA’s scalable and flexible architecture ensures systems can adapt and grow without needing significant overhauls. This adaptability is critical to future-proofing industrial operations and embracing emerging trends like machine learning and artificial intelligence in manufacturing processes.
The role of OPC UA in OT environments is multifaceted and far-reaching. Its ability to bridge different industrial hardware and software, standardize data exchange, and drive intelligent operations places it at the forefront of industrial automation and Industry 4.0 initiatives. By leveraging OPC UA, industries can achieve greater integration, efficiency, and intelligence in their operations, paving the way for more advanced, connected, and innovative industrial ecosystems.
The Imperative of ICS Cybersecurity

Emerging Cyber Threats in OT
Integrating internet-connected technologies in Operational Technology (OT) environments has significantly amplified their exposure to cyber threats. This digital transformation, while bringing numerous benefits in terms of efficiency and connectivity, also opens the door to various sophisticated cyber threats. This section delves into the evolving nature of these threats, illustrating their potential impact on Industrial Control System (ICS) environments and industrial operations’ overall safety, reliability, and efficiency.
Notable Incidents and Their Implications
Stuxnet and Beyond: The attack targeting nuclear facilities was a watershed moment in industrial cybersecurity. It demonstrated how cyber threats could leap from the digital realm and cause tangible, physical harm. Since Stuxnet, there have been numerous other incidents, each underscoring different vulnerabilities in ICS environments. These incidents highlight the need for robust cybersecurity measures that adapt to evolving threats.
Expanding Attack Surfaces: The growing integration of IoT devices, cloud computing, and wireless technologies in OT environments has boosted the potential attack surfaces. If not adequately secured, each connected device or system can be an entry point for cyber attackers, making securing OT environments increasingly complex.
Spectrum of Cyber Threats
Data Breaches: Like a trojan horse in the digital age, unauthorized access to sensitive data can wreak havoc. For industries, a breach could expose the lifeblood of their operations: proprietary manufacturing processes, customer information, or strategic plans.
Espionage: The shadow of industrial espionage looms large. It involves the stealthy theft of critical information for competitive advantage. This could mean pilfering unique manufacturing techniques or sensitive infrastructure details ripe for exploitation in the OT landscape.
Sabotage: Sabotage in OT can morph into various forms, from insidious tampering with production lines to outright equipment malfunctions. Similar to digital vandalism, these acts disrupt operations and can lead to hazardous scenarios, jeopardizing employees and the environment.
Operational Disruption: Cyberattacks are the modern-day gremlins in industrial processes’ machinery. They can cause minor inconveniences and significant operational downtime, impacting production schedules, delivery timelines, and, ultimately, the financial bottom line.
Impact on Safety, Reliability, and Efficiency
Safety Risks: In sectors like chemical plants or power stations, cyberattacks could create scenarios endangering workers and public safety. Imagine manipulating control systems in a chemical plant, resulting in a hazardous material leak – a digital mistake with real-world peril.
Compromised Reliability: In industrial operations, reliability is not just a virtue but a necessity. Cyber threats that lead to unexpected downtime or system failures can shake the foundation of trust in these systems, which is paramount for continuous and stable operations.
Efficiency Losses: Industrial operations’ efficiency is intricately linked to the precision and optimization of control systems. Cyber threats that disrupt these systems can create inefficiencies, escalating costs and diminishing the competitive edge.
The emerging cyber threats in OT environments call for a proactive and comprehensive approach to cybersecurity. Understanding the multifaceted nature of these threats, their potential impact, and the ever-changing landscape is crucial for industries to fortify their defenses. This requires a blend of advanced technological solutions and a strategic shift in cybersecurity approach, focusing on resilience, adaptability, and continuous improvement in the face of rapidly advancing cyber threats.
Importance of ICS Cybersecurity

In the vast and complex industrial landscape, the significance of Industrial Control System (ICS) cybersecurity stands as a lighthouse, guiding the safety of critical infrastructures against an ocean of threats. This section explores the many facets of ICS cybersecurity, emphasizing its role in protecting the nervous system of industrial processes – the networks, devices, and control systems.
Protecting Core Industrial Networks and Devices
Shielding Network Infrastructure: Industrial networks are like the vital arteries of communication in ICS environments. Protecting them from cyber threats is essential to prevent unauthorized access and ensure the integrity of data transmission across the system.
Securing Control Devices: Devices like sensors, actuators, and PLCs (Programmable Logic Controllers) are sentinels for monitoring and controlling industrial processes. Ensuring their cybersecurity is vital to prevent manipulation or disruption of these devices, which could have catastrophic consequences.
Ensuring Operational Continuity
Minimizing Downtime: Cybersecurity incidents can be disruptive, leading to significant operational downtime. An effective ICS cybersecurity strategy is pivotal to preventing such occurrences and ensuring that the gears of industrial processes run smoothly and without interruption.
Resilience Against Attacks: As cyber threats evolve, ICS environments must be fortified enough to withstand sophisticated attacks. This involves defensive measures and the ability to swiftly recover from incidents, maintaining the lifeblood of operational continuity.
Maintaining Safety Standards
Worker and Public Safety: Many industrial processes involve materials or conditions that, if tampered with, could endanger workers and the public. ICS cybersecurity measures prevent such scenarios.
Preventing Catastrophic Events: Cybersecurity energy, water treatment, and chemical manufacturing breaches could trigger catastrophic events. Robust ICS cybersecurity acts as a bulwark to avert such calamities, safeguarding the environment and public health.
Upholding the Integrity of Industrial Processes
Data Integrity and Accuracy: Accurate data is the beating heart of optimal operation in industrial processes. Cybersecurity measures ensure that this data is reliable and uncorrupted, a critical component for decision-making.
Quality Control: The integrity of industrial processes is directly tied to the quality of the product. ICS cybersecurity is crucial in maintaining this integrity, ensuring the control processes are unbroken and untainted.
Compliance and Legal Considerations
Regulatory Compliance: Navigating the seas of stringent regulatory requirements regarding cybersecurity is essential. Compliance avoids legal entanglements and ensures adherence to the highest standards of cybersecurity.
Protecting Intellectual Property: Industrial setups are often treasure troves of proprietary technology and trade secrets. ICS cybersecurity is the guardian of this intellectual property, shielding it from the prying eyes of cyber espionage and theft.
In the grand scheme of modern industrial operations, ICS cybersecurity is monumental. It extends beyond mere protection against cyber threats; it encompasses ensuring operational continuity, maintaining safety standards, upholding process integrity, and meeting compliance requirements. As industrial systems continue to evolve and intertwine more deeply with digital technologies, the role of ICS cybersecurity becomes ever more critical, demanding unwavering vigilance, adaptation, and enhancement to stay abreast of the evolving threat landscape.
Integrating OPC UA with ICS Cybersecurity

Enhancing Security with OPC UA
Open Platform Communications Unified Architecture (OPC UA) is not just a conduit for seamless data exchange; it is also a bastion of robust security features designed to enhance the cybersecurity posture of industrial environments. These inherent features address various security aspects, from fortifying data in transit to ensuring only authorized entities can access critical systems. This section delves into a detailed exploration of these essential features of security of OPC UA and their roles in fortifying industrial control systems.
Encryption for Securing Data in Transit
Data Confidentiality: OPC UA wields sophisticated encryption techniques to shield data during transmission between devices and systems. This encryption is a cloak of invisibility, ensuring sensitive information remains confidential and impervious to unauthorized entities.
Protection Against Eavesdropping and Man-in-the-Middle Attacks: The encryption fortress of OPC UA stands tall against the threats of eavesdropping and man-in-the-middle attacks, where malicious entities could intercept or alter data during its voyage.
Authentication Protocols to Verify Identities
Device and User Authentication: OPC UA erects a stronghold of robust authentication mechanisms to ascertain the identities of both users and devices. This process is the gatekeeper, ensuring only legitimate entities can engage with the system.
Different Levels of Authentication: OPC UA offers a spectrum of authentication, from the simplicity of username-password schemes to the sophistication of certificate-based methods. This versatility allows tailoring a security level that fits the operation’s risk profile.
Authorization Mechanisms to Control Access
Role-Based Access Control (RBAC): OPC UA employs the role-based access control strategy, delineating the resources a user or device can access within the system. This ensures that entities only wield powers appropriate to their roles and permissions.
Fine-Grained Access Control: OPC UA allows for meticulous access control, empowering administrators to specify exact permissions for each user or device, down to individual data points or functions.
Audit Trails for Accountability and Traceability
Tracking User and System Activities: OPC UA maintains detailed logs of all activities, chronicling who accessed the system, the actions performed, and the timestamps of these actions. This audit trail is the scroll of accountability.
Forensic Analysis and Compliance Reporting: In a security incident, these audit trails become invaluable for forensic analysis, unraveling the tapestry of what transpired and how to prevent future incidents. Furthermore, these logs are often critical for compliance with various regulatory standards demanding detailed reporting of access and activities.
The security features embedded in OPC UA form a formidable defense in enhancing the cybersecurity of industrial environments. These features collaborate to provide comprehensive protection, ensure data confidentiality, verify identities, control access, and maintain traceability. By harnessing these security capabilities, organizations can significantly bolster their defenses against various cyber threats, safeguarding their critical industrial operations.
Best Practices for Secure OPC UA Deployment
Deploying Open Platform Communications Unified Architecture (OPC UA) in industrial environments demands a comprehensive approach to security. The following best practices are pivotal in ensuring that OPC UA deployments facilitate effective communication and data exchange and stand resilient against potential cyber threats.
Network Segmentation: Reducing the Attack Surface
Defining Clear Boundaries: Segmenting networks involves crafting clear demarcations between Operational Technology (OT) and Information Technology (IT) networks. This strategic separation minimizes the pathways that cyber attackers can exploit to infiltrate critical control systems.
Limiting Propagation of Threats: By creating these segmented networks, any potential breach or cyber threat in one domain (e.g., the IT environment) can be contained, preventing its spread to the OT realm where it could wreak more significant havoc.
Firewalls and DMZs: Controlling and Monitoring Traffic
Implementing Firewalls: Firewalls serve as vigilant sentinels, controlling traffic flow between network realms. They are instrumental in scrutinizing incoming and outgoing traffic, thwarting unauthorized access, and repelling malicious endeavors.
Establishing Demilitarized Zones (DMZs): DMZs act as the buffer territories between the external network (internet) and the internal sanctums (OT and IT). They typically house devices and services that necessitate accessibility from internal and external networks, adding a layer of security.
Regular Patching and Updates: Keeping Systems Current
Routine Maintenance: Consistently updating and patching OPC UA servers and clients is vital for repairing known vulnerabilities. This maintenance is a shield, preventing attackers from exploiting archaic software, a common pathway for cyber invasions.
Staying Informed: Keeping abreast of the latest security patches and updates from OPC UA developers and promptly implementing them ensures the system is fortified against newly unearthed threats.
Robust Access Control: Safeguarding System Integrity
Implementing Role-Based Access Control (RBAC): RBAC is akin to assigning specific roles in a royal court. It ensures users only access resources necessary for their designated role, minimizing the risk of accidental and intentional system misuse.
Strong Authentication Methods: Implementing multi-factor authentication and robust password policies elevates the security of user accounts, significantly reducing the likelihood of unauthorized access.
Continuous Monitoring: The Art of Proactive Detection and Response
Real-Time Monitoring: Constant vigilance in monitoring network traffic and system activities enables early detection of unusual patterns or anomalies, which could signal a cybersecurity threat.
Incident Response Planning: A robust incident response plan is like a well-rehearsed orchestra, ensuring any detected anomalies are addressed swiftly and effectively, minimizing potential disruptions or damage.
The security of OPC UA deployments in industrial settings requires a multi-faceted, layered approach. Network segmentation, the strategic use of firewalls and DMZs, regular software updates, stringent access controls, and continuous monitoring constitute a robust cybersecurity strategy. By adhering to these best practices, organizations can significantly enhance the security and resilience of their OPC UA deployments, thereby protecting them from a spectrum of cyber threats.
Addressing Challenges in OPC UA and ICS Cybersecurity
Implementing Open Platform Communications Unified Architecture (OPC UA) in Industrial Control System (ICS) environments presents unique challenges that stem from the need to integrate legacy systems, bridge the skill gap in the workforce, and ensure compliance with industry standards and regulations. Addressing these issues is crucial for the successful deployment and operation of OPC UA in industrial settings.
Legacy Systems Integration
Compatibility Issues: Many OT environments function with legacy systems, relics of a bygone era, which may not readily align with the modernity of OPC UA. These systems might utilize outdated protocols and technologies, posing challenges for direct integration.
Innovative Integration Solutions: Addressing the integration of legacy systems often requires creative solutions. This might involve developing bespoke middleware or utilizing protocol gateways that translate between legacy protocols and OPC UA.
Careful Planning and Phased Implementation: Integrating legacy systems with OPC UA demands meticulous planning. A phased approach, where legacy systems are gradually incorporated or upgraded, can minimize disruptions to ongoing operations.
Testing and Validation: Thorough testing is essential to ensure the integration of legacy systems doesn’t introduce new vulnerabilities or stability issues. This includes assessing the interoperability and performance of the integrated systems under various operational conditions.
Bridging the Skill Gap
Cross-Disciplinary Expertise: Effective deployment and management of OPC UA in ICS environments necessitate professionals proficient in OT and IT, particularly cybersecurity. This blend of knowledge is crucial to understanding industrial systems’ intricacies and the cybersecurity threats they face.
Training and Education Programs: To bridge the skill gap, it is imperative to invest in training programs for existing staff and incorporate relevant coursework into educational institutions. These programs should focus on the convergence of IT and OT, emphasizing the unique cybersecurity challenges in industrial environments.
Hiring and Development Strategies: Organizations may need to devise targeted hiring strategies to attract talent with the proper skill set. Furthermore, nurturing a culture of continuous learning and professional development can aid existing employees in adapting to the evolving technological landscape.
Regulatory Compliance
Adhering to Standards: Compliance with industry standards and regulations, such as IEC 62443, is a legal formality and critical for operational efficiency and security. These standards provide guidelines for securing industrial automation and control systems.
Regular Compliance Audits: Conducting comprehensive audits regularly can assist organizations in assessing their adherence to relevant standards and regulations. These audits should be all-encompassing, covering every aspect of the OPC UA deployment, from system design and implementation to ongoing operations.
Staying Current with Regulatory Changes: The landscape of regulations and standards in cybersecurity and industrial automation is ever-evolving. It is vital to stay informed about these changes and adjust practices accordingly to remain compliant.
Integrating legacy systems, bridging the skill gap, and ensuring regulatory compliance are crucial for implementing OPC UA in ICS environments. This requires a blend of technical innovation, strategic workforce development, and a steadfast commitment to compliance and best cybersecurity practices. By confronting these challenges head-on, organizations can fully leverage the potential of OPC UA, enhancing their industrial operations’ security, efficiency, and reliability.
Conclusion: Embracing the Future with OPC UA and Enhanced ICS Cybersecurity

Integrating Open Platform Communications Unified Architecture (OPC UA) into Operational Technology (OT) environments is a significant milestone in the saga of industrial automation. This advancement is not merely a step forward; it represents a transformative leap in how industrial systems communicate, operate, and shield themselves against an ever-complex tapestry of cyber threats. This conclusion contemplates the broader implications of this integration for the industrial sector, emphasizing the strategic necessity of adopting OPC UA in tandem with robust ICS cybersecurity measures.
Unprecedented Interoperability and Efficiency
Seamless Integration: OPC UA’s role in enabling interoperability across diverse industrial systems and platforms is akin to a master key unlocking doors to seamless data exchange and communication. This breaks down historical barriers that have traditionally hampered industrial operations.
Efficiency in Operations: With OPC UA, industries can achieve new levels of operational efficiency. The standardized communication model, coupled with the ability to manage complex data types, streamlines processes, reduces errors, and bolsters decision-making capabilities.
Addressing the Cybersecurity Imperative
Navigating the Threat Landscape: The advent of OPC UA spotlights the critical need for robust ICS cybersecurity. As industrial systems become more interconnected and exposed to digital realms, their cyberattack vulnerability increases. This new reality demands heightened vigilance in securing these systems against potential breaches.
Comprehensive Security Measures: Ensuring ICS systems’ cybersecurity in the OPC UA era necessitates a layered approach. This includes harnessing OPC UA’s built-in security features and adopting industry best practices like network segmentation, regular patching, stringent access controls, and continuous monitoring.
A Strategic Necessity in the Modern Industrial Landscape
More Than a Technological Upgrade: Adopting OPC UA in industrial environments transcends the concept of a simple technological upgrade. It is a strategic move that aligns with the broader trends of digital transformation and Industry 4.0. This makes industrial organizations agile, resilient, and competitive in a rapidly evolving digital world.
Preparing for the Future: Embracing OPC UA and bolstering ICS cybersecurity is about future-proofing industrial operations. As technologies advance and the fusion of physical and digital worlds accelerates, preparedness and adaptability become crucial. OPC UA offers a framework that addresses current needs while being scalable and adaptable to future technological evolutions.
In conclusion, integrating OPC UA into OT environments is a pivotal development in industrial automation, bringing unparalleled interoperability and efficiency. However, this progress also underlines the critical importance of robust ICS cybersecurity. By gaining a comprehensive understanding of OPC UA and implementing rigorous cybersecurity practices, network experts and engineers are well-equipped to protect industrial systems against complex cyber threats, ensuring operational resilience and reliability. This integration is not just a technological leap; it’s a strategic imperative that will define the future trajectory of industrial operations.










